Introduction
The Trezor login system is built around one core principle: ensuring that only the rightful owner of a Trezor hardware wallet can access its stored cryptocurrency. Unlike online platforms that use conventional email-and-password logins, Trezor relies on a secure, hardware-based authentication process. This approach minimizes exposure to attacks and ensures that private keys remain completely offline.
As more people adopt cryptocurrency, secure access methods have become increasingly important. Trezor aims to provide transparency, safety, and ease of use, giving users the confidence to store and manage their digital assets without relying on third-party services. Understanding how the Trezor login process functions can help users navigate the system correctly and maintain strong protection over their funds.
How the Trezor Login System Is Designed
When logging in, users do not enter credentials online or store them on servers. Instead, the authentication process occurs entirely through the Trezor hardware wallet and the Trezor Suite application. Once the device is connected, Trezor Suite identifies it and prompts the user to enter their PIN directly through a secure method that prevents digital interception.
This PIN entry system is designed to shield sensitive data from keyloggers and malware. Even if the computer being used is compromised, attackers cannot collect the PIN because it never appears in plain text. The Trezor device itself ensures that the PIN is processed securely inside its protected chip.
The Role of the Passphrase
Some users choose to add a passphrase as an extra layer of protection. This optional feature creates an additional “hidden” wallet, accessible only when the correct passphrase is entered. Since the passphrase is never stored on the hardware wallet or any connected device, it provides strong security even if the device is stolen or lost.
Passphrases offer flexibility: users can create multiple passphrase-protected accounts, each functioning independently. This feature is particularly helpful for anyone looking to organize assets or maintain an extra layer of privacy.
Accessing Your Wallet Through Trezor Suite
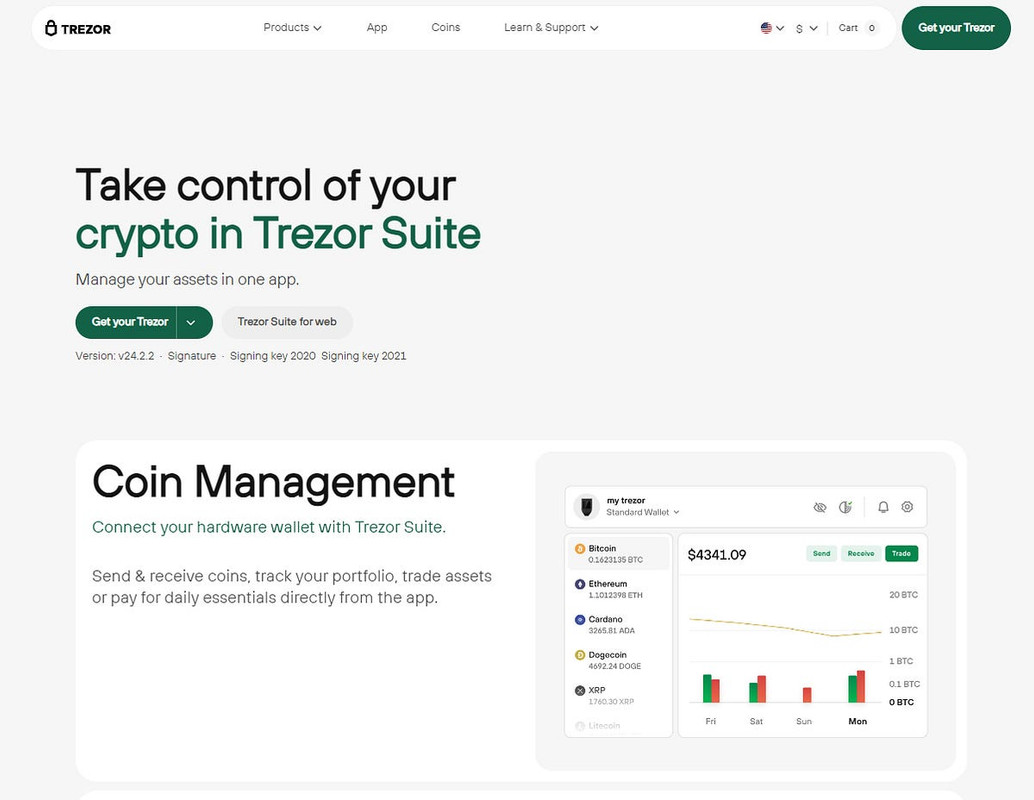
Trezor Suite is the official software interface for interacting with your Trezor hardware wallet. Through the suite, users can manage accounts, track portfolios, view activity, and send or receive funds. The dashboard is designed to offer an intuitive user experience while maintaining high standards of security.
Available for desktop and web usage, Trezor Suite offers flexibility without compromising safety. The desktop version is generally recommended because it reduces potential exposure to browser-based vulnerabilities, but both options include the same core features.
Steps to Complete a Trezor Login
Logging in to your Trezor wallet requires only a few steps. The following guide outlines the basic process:
- Connect your Trezor hardware wallet to your computer or mobile device.
- Launch the Trezor Suite desktop application or access the web version.
- Wait for the Suite to recognize your hardware device.
- Enter your PIN securely using the Trezor interface.
- If enabled, input your passphrase to access the corresponding wallet.
- Once authenticated, review your accounts and manage your crypto assets.
Each step reinforces security by requiring physical confirmation and ensuring that private keys remain isolated from online environments.
Key Security Advantages of Trezor Login
The Trezor login process is designed to offer several strong security benefits:
- Offline private key storage: Keys are never exposed to the internet.
- Secure PIN entry: Prevents interception by malicious software.
- Optional passphrase: Adds an additional protective layer.
- Physical device verification: Ensures the user must be present.
- No online accounts: Eliminates risk associated with stored credentials.
- Device-based approvals: All actions require confirmation on the hardware wallet.
These features combine to deliver a login system that is resilient against unauthorized access, phishing attacks, and data breaches.
Tips for Keeping Your Wallet Safe
Even with strong hardware-based protection, users should follow recommended safety practices. Always download Trezor Suite from the official Trezor website, and keep your wallet’s firmware updated. Never share your recovery seed, and store it securely offline. Using a passphrase can further strengthen account protection.
Avoid connecting your Trezor device to unfamiliar computers, and verify all transactions directly on the device screen before approving them. These steps help ensure that your login process remains secure and your crypto assets stay protected.
Conclusion
The Trezor login system provides a reliable, secure foundation for managing cryptocurrency through a hardware wallet. By combining offline authentication, physical verification, and an intuitive software interface, Trezor ensures that only the rightful owner can access stored funds. Whether you are new to digital assets or experienced in crypto management, Trezor’s login process offers clarity, confidence, and strong protection.
With safety built into every step, users can navigate the world of cryptocurrency with assurance, knowing that their access method is secure and designed to protect long-term digital wealth.